Scope, priority, and decisions
Primary question: what can enter the MVP, what is gated, and what still needs approval?
Output: PRD scope, release phase, and decision owner list.This site is the English source for internal development. It gives product owners the scope, frontend UI teams the interface direction, backend engineers the business objects and rules, chief engineers the system logic, marketing the narrative, brand teams the visual direction, and customer experience teams the user value.
This site is not a loose document archive. It is a role-based workbench with clear questions, deliverables, and review standards for each team.
Confirm scope, priorities, page entry points, MVP phases, and open product decisions.
View product boundaries Frontend UIUnderstand page structure, component rhythm, status chips, asset marks, and navigation hierarchy.
View interface direction Product DesignTurn identity, assets, payments, credentials, IBC, and Vault into one coherent user experience.
View design logic BackendUnderstand the boundaries for account, receipt, credential, invoice, policy, and audit objects.
View API needs Chief ArchitectCheck whether modules, permissions, risk gates, and future expansion share one system logic.
View system logic MarketingExplain in plain language that this is a trusted digital account, not a conventional wallet.
View narrative frame BrandUnify the M mark, FCA, USDF, MXCD Future, and the green identity system into one visual family.
View brand direction Customer ExperienceIdentify the real advantages: trusted identity, recoverable wallet access, clear payments, complete records, and closed service loops.
View experience valueUse this as the meeting map. It tells each team where to start, which sections to use next, and what output they should produce before work moves forward.
Primary question: what can enter the MVP, what is gated, and what still needs approval?
Output: PRD scope, release phase, and decision owner list.Primary question: how should identity, trust, risk, records, and account context appear on screen?
Output: page state map, component set, and screen flow updates.Primary question: which domain objects, checks, events, and failure states are required?
Output: service boundaries, state machines, event list, and API draft.Primary question: how do we explain the wallet without overpromising USDF, MXCD, or government status?
Output: approved language for partners, government, website, and decks.Primary question: where might users get confused, blocked, anxious, or need help?
Output: help scripts, recovery guidance, escalation rules, and experience risks.This map prevents features from becoming isolated descriptions. If a feature cannot be traced across these columns, it needs more product work.
mid, account, device_sessionmpc_policy, recovery_casepayment_request, receiptcompany, role, invoicecredential, proof_requestquote, vault_card, signing_sessionnetwork_adapter, chain_txThis section turns the product vision into a working release board. A module is not ready until the page, policy rule, backend object, receipt or audit event, and team handoff are all clear.
Verified MID, selected account, device session, passkey / biometric state, and MID Card binding.
Daily signing, device share model, recoverable access, risk checks, cooling period, and security notices.
Primary FC Chain balances, receive, send, fee display, network state, and transaction receipt.
QR contact, payment request, note, simple confirmation, receipt detail, and payment timeline.
Company account switcher, role checks, signed invoices, service payment, and company receipt archive.
MID card, address proof, tax number, IBC certificate, proof QR, and selective credential sharing.
Controlled FC ecosystem swap, quote policy, large-operation Vault signing, and protected asset flows.
BTC, ETH, TRON, SOL, and BNB balance view, receive, send, confirmations, and risk prompts.
Do not reduce M Wallet to an asset list. First help users understand their MID status, account context, and recovery posture. Assets, payments, IBC, credentials, and services should then appear as verified account capabilities.
The user owns or applies for a MID first. Sensitive actions and wallet recovery are linked to MID status, MID Card proof, account context, device session, and risk state.
The account is the container. Personal and company accounts carry different balances, roles, receipts, permissions, and service records.
Verified identity unlocks payments, payment requests, Credential Center, official notices, and service payments.
Daily wallet control is recoverable through MID-based MPC policy; Swap, high-value payments, company reserves, credential sharing, and future MXCD require stricter policy rules and Vault Card protection.
FCA, USDF, MXCD Future, and external assets serve different product roles. The interface should make those roles obvious instead of treating everything as a flat token list.
FC Chain's native asset represents network fuel, infrastructure, and the ecosystem base. Its visual language should stay calm navy plus soft champagne.
A USD-denominated payment rail for early payments, service payments, and receipt-based settlement experience. It should feel stable, friendly, and easy to use.
A future settlement asset concept with stronger sovereign characteristics. It should be presented as a future rail only, without implying formal availability today.
BTC, ETH, TRON, Solana, and BNB Chain support balance view, receive addresses, and sending. They belong in the secondary wallet layer and should not enter Swap or dominate the product story.
This is the core module map for development. Every module must answer: who is the user, which account is active, which actions are allowed, and what record is produced.
MID status, account switching, balance overview, quick actions, pending requests, and official alerts.
FCA, USDF, MXCD Future, external assets, receive, send, and Vault status.
USDF/FCA quote, rate, fee, policy check, confirmation, and receipt.
QR contacts, payment requests, notes, receipts, and confirmations without open-ended chat.
Company accounts, roles, invoices, receipts, service records, and company reserves.
Digital ID, driver license, address proof, tax number, company certificates, and proof QR.
NFC cold signing, high-value payments, company reserves, backup cards, and lost-card handling.
Official broadcasts, signature verification, renewal reminders, security alerts, and deep links.
Official invoices, payment rails, role verification, payment confirmation, and record archive.
Devices, Passkey, biometrics, limits, recovery method, and notification preferences.
Use this as the bridge between product design and engineering. If a row is incomplete, the feature is not ready for implementation.
user, mid, account, device_sessionmpc_policy, device_share, recovery_caseasset_balance, address, transaction, receiptcontact, payment_request, message, receiptswap_pair, quote, execution, policycompany, role, invoice, service_recordcredential, issuer, proof_request, consentmid_card, signing_payload, auth_eventvault_card, signing_session, protected_assetbroadcast, issuer_signature, notificationnetwork_adapter, external_address, chain_txThis layer turns the guide into a release-quality checklist. It helps product owners decide what can enter sprint planning, helps engineering see contract boundaries, and helps QA know what must be verified.
Use this as the meeting view before a feature enters PRD, UI design, backend design, or sprint planning.
Identity state, account switcher, device session, MID Card binding, and audit event are defined.
Recovery is a product advantage, but thresholds, review levels, and support scripts still need approval.
Primary rails are clear; build must include fees, confirmations, receipts, and risk prompts.
Payment request, note, confirmation, and receipt are defined as structured communication only.
Company wallet logic is clear; first service set and role approval rules need product sign-off.
Core cards, proof sharing, consent, expiry, issuer signature, and audit record are defined.
Concept and policy boundary are clear; implementation should wait until account and risk model are stable.
View, receive, and send are required; launch networks, limits, fees, and confirmation rules need finalization.
Every critical flow should be testable as a user journey, a policy check, and a backend record.
This is not the final API spec. It is the contract boundary that tells engineering what each module must expose, validate, emit, and fail with.
user, mid, account, asset_balance, transaction, receipt, credential, invoice, audit_event
pending, verified, suspended, blocked, requires_step_up, signed, broadcasted, completed, failed
MID active, selected account, role permission, device trust, quote validity, issuer signature, network availability, risk threshold, Vault requirement.
mid.verified, account.switched, payment.completed, receipt.created, recovery.opened, vault.signed, broadcast.read
MID_REQUIRED, ACCOUNT_FORBIDDEN, ROLE_DENIED, QUOTE_EXPIRED, NETWORK_UNAVAILABLE, VAULT_REQUIRED, ISSUER_UNVERIFIED
All sensitive actions need idempotency, policy result, human-readable summary, audit event, and user-facing receipt or security notice.
This layer gives design and frontend teams a shared component language. Every screen should express identity, account context, trust status, risk state, and record outcome in a consistent way.
Shows Personal, IBC, and future Vault context before sensitive actions. It prevents paying or signing from the wrong account.
Required on Home, Wallet, Pay, IBC, and Settings.Uses short labels for Verified, Pending, Policy, Blocked, Signed, Future, and Expired. Chips must never replace explanatory text for blocked actions.
Use with credentials, invoices, accounts, and transactions.Separates primary FC Chain rails from secondary external assets. FCA and USDF should appear before external networks.
Show asset role, network, balance, send, receive, and receipt entry.Card-style credential storage for MID, Address Proof, Tax Number, IBC Certificate, and future official cards.
Always show issuer, validity, proof action, and sharing scope.Receipts are proof of product trust. They should cover payments, swaps, service invoices, credential sharing, and security actions.
Show timestamp, account, asset, counterparty, status, and export entry.Supports payment request, note, receipt, and simple confirmation. It should not become open-ended social chat.
Show verified counterparty, amount, rail, note, and confirmation state.Official notices must feel signed, verified, and actionable without looking like marketing push messages.
Show issuer, signature state, priority, channel, and deep link target.Explains why an action needs MID Card, Vault Card, MPC recovery, role approval, or a waiting period.
Use for blocked, high-value, recovery, and policy-gated flows.Each page should be designed with its empty, normal, pending, blocked, risk, and success states before production UI starts.
No MID, review pending, verified, IBC available, payment request pending, official notice, security alert.
No assets, FCA / USDF active, external assets enabled, receive address, network degraded, Vault required.
No contacts, QR contact added, request pending, paid, failed, receipt ready, counterparty not verified.
No company, linked company, role missing, signed invoice due, payment pending, paid and archived.
No credential, issued, expired, shareable, shared, revoked, MID Card tap required.
No pairs, quote loading, quote expired, policy blocked, preview, completed, receipt available.
Trusted device, new device, recovery opened, cooling period, review required, Vault Card unbound.
No messages, unread official notice, verified invoice, action required, archived, issuer unverified.
Risk states must be understandable, actionable, and auditable. Never ask users to sign or pay without a human-readable explanation.
Always show reason, next step, and whether the user can resolve it alone.
High-risk signing must show amount, asset, account, counterparty, network, and purpose.
MID Card proves identity; Vault Card protects high-value signing. UI copy must keep them distinct.
Every payment, swap, recovery, credential share, and official action needs a visible record path.
The interface should feel fresh, light, and trusted. It should not feel like an exchange, a heavy government portal, or a speculative crypto app.
The lab compares Fresh Finance, Living Wallet, Civic Trust, MID-First Identity, and FC Ecosystem Wallet routes without changing the official guide too early.
Verified · Montserrat Digital ID
Total assets
Personal account · FC Chain
Amina Joseph · 250 USDF · verified MID
This new column brings the Montserrat Digital Identity Card design manual into the M Wallet team site. It connects the wallet's MID-first product logic with the physical credential, visual system, FC Chain verification layer, and production checklist.
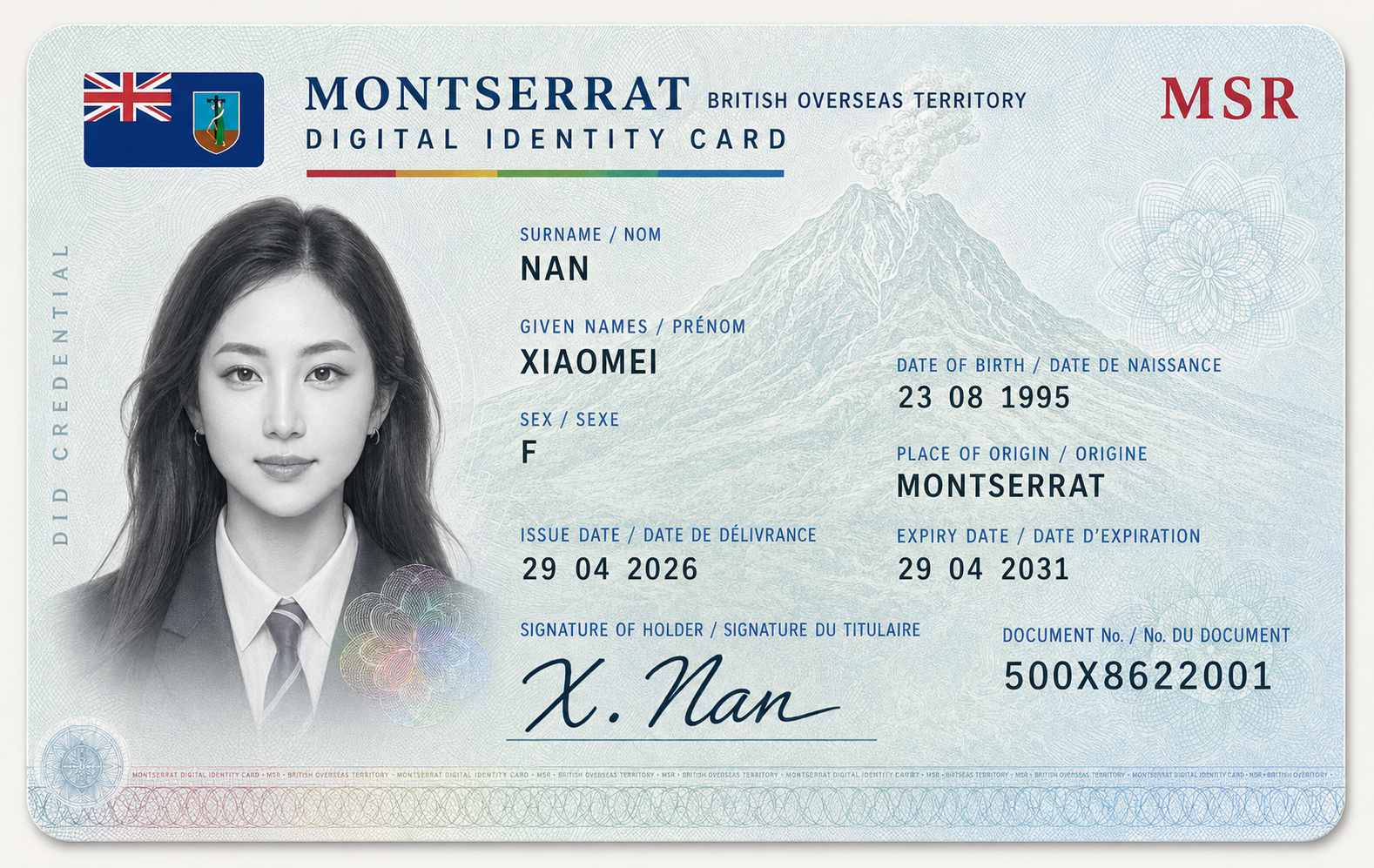
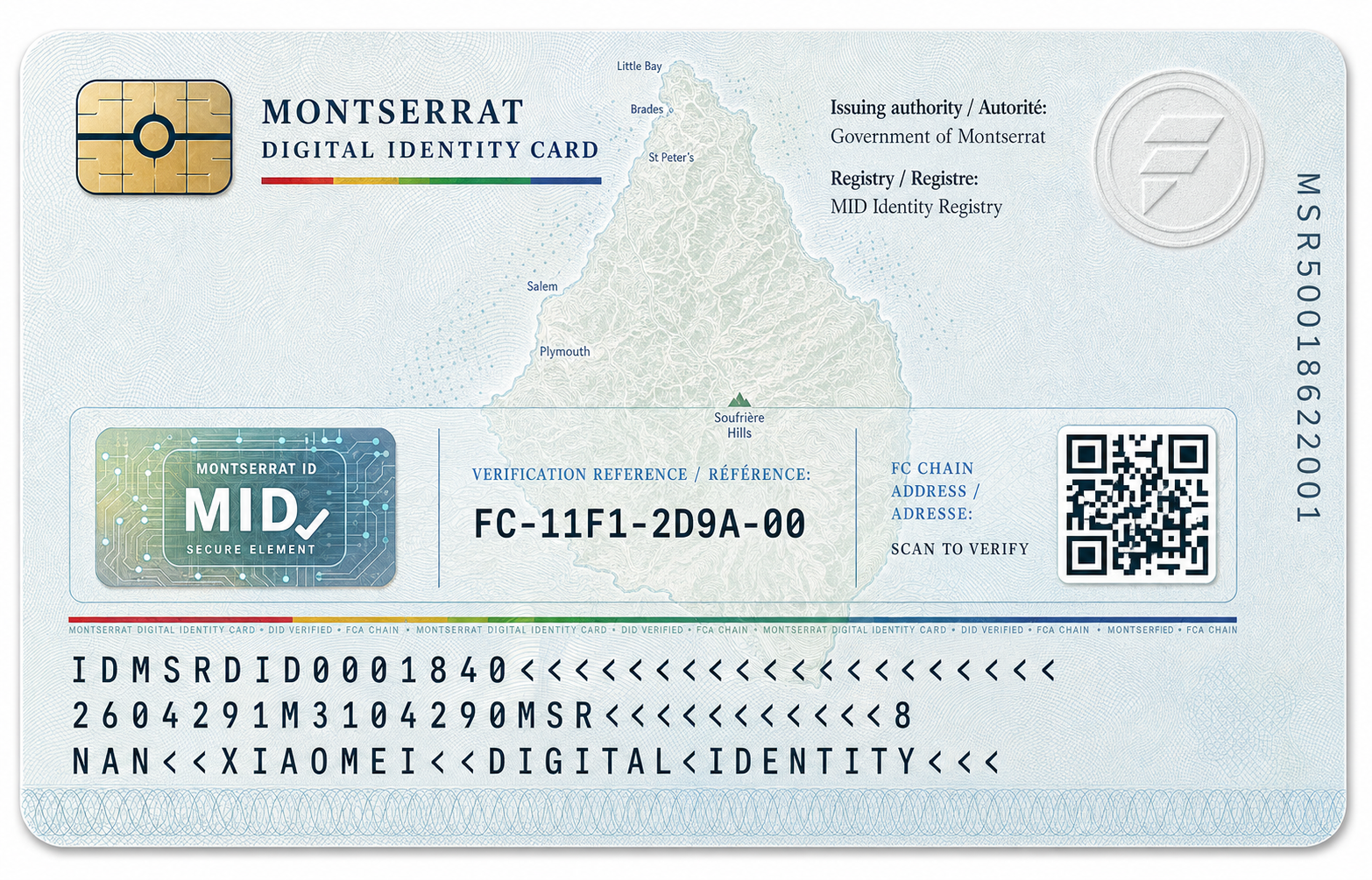
The manual now lives inside this website as a team reference. Product, design, brand, engineering, and CX teams can use it to align on what appears on the card, what stays digital, how FC Chain verification is presented, and how the document keeps a government-grade tone.
Only essential identity, issuance, origin, signature, document number, and verification cues belong on the physical credential.
Light Caribbean security paper, accurate Montserrat geography, integrated portrait, restrained security texture, and official document hierarchy.
QR should resolve to the DID / FC Chain verification address, while MRZ and serial fields stay readable and non-overlapping.
Map location, privacy fields, FCA watermark, QR spacing, MRZ density, header hierarchy, and print-readiness must pass before release.
The core engineering objects are not tokens alone. They are user, MID, account, MPC policy, recovery case, credential, invoice, receipt, policy, and audit event.
user_id, mid_id, credential status, device sessionrecovery_case_id, device shares, MID Card proof, risk scoreaccount_id, account type, roles, policy profileThese cards are the working checklist for each team when reviewing this guide.
These journeys show how identity, account context, payment, credentials, and records work together. They are also a practical checklist for product, design, backend, QA, marketing, and customer experience teams.
The user verifies MID, binds MID Card, creates the daily MPC wallet, receives FCA / USDF, and sees the first receipt.
Two MID users add each other by QR, exchange a structured payment request, add a note, pay in USDF or FCA, and keep receipts.
A company operator switches to the IBC account, opens a signed invoice, passes role checks, pays, and archives the service receipt.
The user proves MID ownership, uses MID Card and risk checks, passes the recovery policy, and restores wallet access without exposing private keys.
The user opens Credential Center, selects address proof or tax number, reviews the sharing scope, and generates a limited proof QR.
A high-value send, company reserve movement, or protected swap triggers Vault policy and asks the user to tap the NFC Vault Card.
External storytelling can be simpler, but it must not drift away from the internal product logic: MID-first, verified account, trusted payment, official records.
M Wallet turns a verified MID into a trusted digital account for payments, credentials, company services, and secure asset control.
Users do not lose assets just because they forgot a seed phrase or lost a device. MID-based MPC recovery keeps wallet access recoverable while still controlled by strict identity and risk checks.
Do not present M Wallet as a high-yield wallet, trading tool, speculative stablecoin product, or already approved sovereign currency system.
MID verification completion, wallet creation completion, MID Card binding, MPC recovery setup, Passkey and biometric binding rate.
First receive, payment request creation, payment completion, receipt view rate.
IBC account binding, official invoice open rate, service payment completion, receipt export rate.
This is not a signal to build every feature at once. First prove the product logic with a working loop, then expand into complex assets and advanced security.
MID status, account switching, FCA/USDF balances, receive, basic receipts, and notification entry.
QR contacts, payment requests, payment notes, receipts, confirmation messages, and Pay timeline.
Company accounts, role rules, official invoices, service payments, and company receipt archive.
Controlled Swap, Vault Card, external asset view/receive/send, and future MXCD policy gate.
This log keeps unresolved questions visible without letting them blur the product direction. Each item has a recommended default, risk, owner, and next action.
This is no longer a plain file list. It is the working navigation for the M Wallet team, giving product, design, engineering, brand, market, government, and customer experience teams a shared way into the same product logic.
Read this team guide first to understand the product north star, then enter the role-specific references. Every reference stays paired in EN / Chinese, with English as the source site and Chinese as the mirror for internal and external communication.
The current package covers product logic, screen storyboard, function manual, engineering spec, interactive prototype, government architecture, asset marks, and ecosystem brand.
Confirm scope, MVP phase, permission rules, core flows, and open decisions before splitting PRD work.
Use the screen storyboard and interactive prototype to understand layouts, states, and scenarios for each feature page.
Use the engineering spec to organize accounts, MID, MPC, credentials, receipts, audit trails, and permission models.
Review M Wallet, FCA, USDF, MXCD, and ecosystem relationships so asset hierarchy and mark usage stay consistent.
Use the government architecture page to align external language around MID-first, trusted accounts, official services, compliance boundaries, and future policy gates.
Use the manual and storyboard to explain the user advantages: identity recovery, receipts, official notices, credential center, and secure signing.
Use this library when you need a specific EN / Chinese paired document.